Obtaining notifications from threats
 Larry
All-Knowing Sage ✭✭✭✭
Larry
All-Knowing Sage ✭✭✭✭
I learned late yesterday afternoon that a client's TZ600 was engaged in threat detection and GAV was doing the blocking.
Below is an excerpt of a screen capture from the Threats Session Logs section in Capture Security Center's Analytics module:
Based on some analysis, this series of events started at approximately 9:30 am and end right before 6:00 pm. In all, 338 alerts were issued.
I'd like to know if there is some way, say after 25 entries, that I could receive an email letting me know that something not necessarily good is going on at the site?
In this case, my client received an email in his "info" account and deleted it. For the rest of the day, the account was unable to connect to the O365 Exchange server.
To solve this, I renamed the OST file and let Outlook recreate it - apparently without the "bad" now delete file.
Just the same, I would really have wanted to have known by 10:00 am that there was a potential problem. Not at 4:30 when my client - exasperated at the end of the day - called me to complain.
Thanks!
Best Answer
-
CORRECT ANSWER
 daniel_lilja
Enthusiast ✭✭
daniel_lilja
Enthusiast ✭✭
Hi Larry,
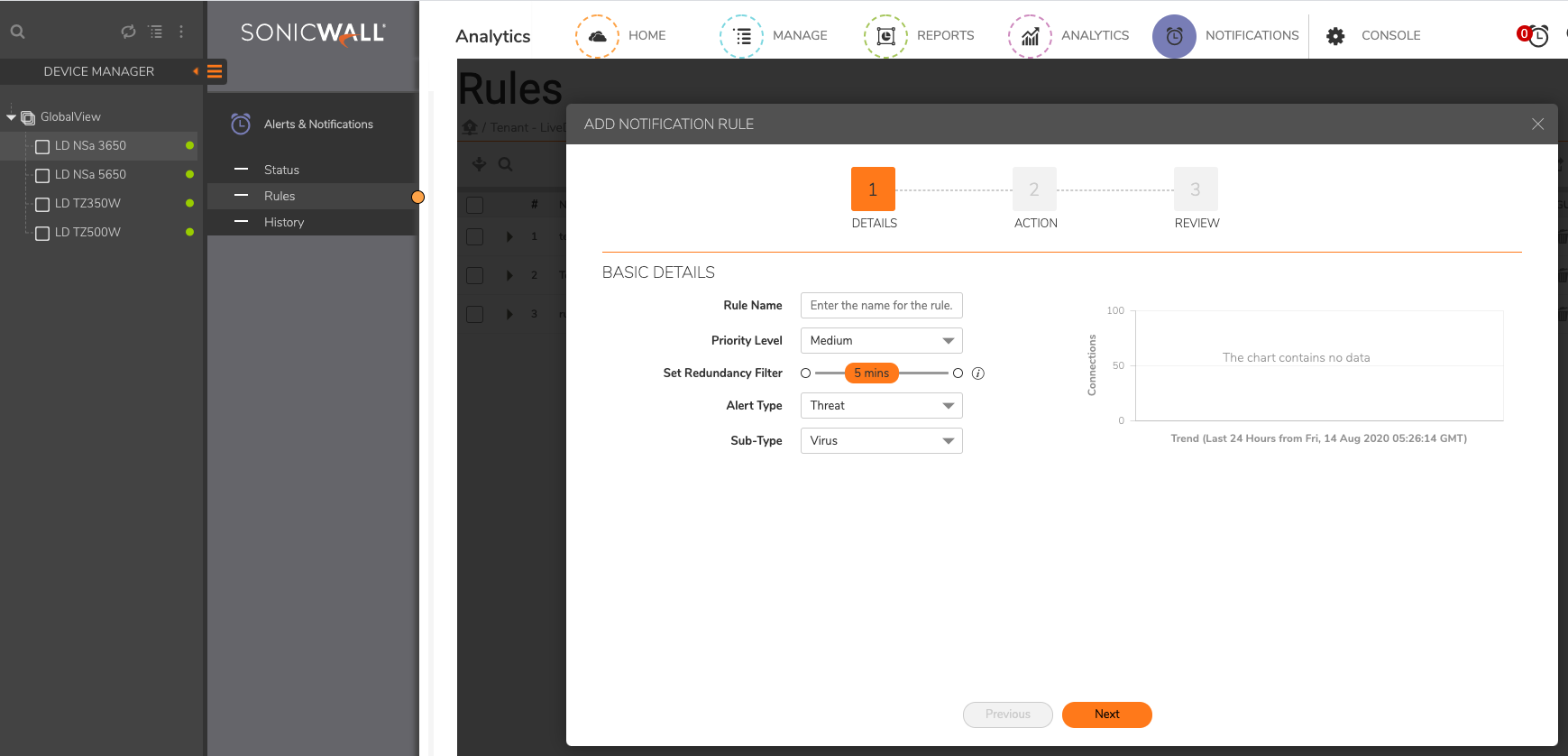
you can configure that via: Notifications -> Select Firewall -> Rules.
I havent find a way to do this Globaly instead of per firewall neither in cloudgms or the NSM 2.0. Does someone know if thats possible? To Configure Alerts/Notifications for all the firewall in the tenant?
5



Answers
Thanks, that works - except for the threshold part. I guess if I had that set, I would have received 300+ emails over the course of the day.
Unanswered in the documentation is what the "Priority level" means. Is it supposed to match the purported threat level priority?
And as far as a global solution, NSM 2.0 is supposed to have templates, but I believe that is for device configuration only. If not available for this, it's going to require an RFE for version 2.5...